What Is Software RCSDASSK?
In 2026, one term that keeps appearing across IT forums, enterprise tech blogs, and developer communities is software RCSDASSK. Despite its unusual name — which reportedly stands for Remote Control System for Data Automation, Security, and Software Kit — the platform represents a serious shift in how businesses and technical teams manage their digital operations.
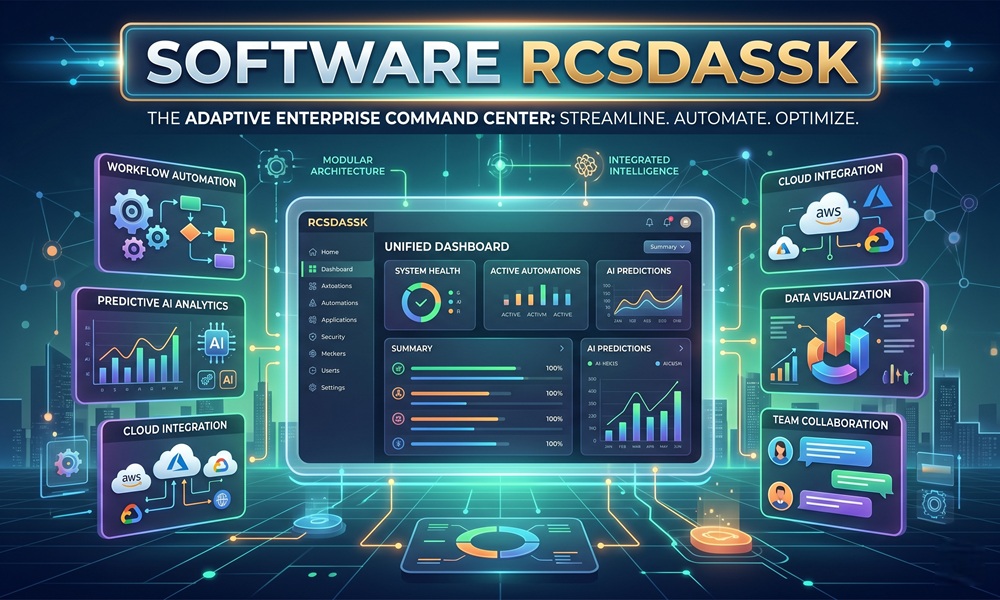
At its core, software RCSDASSK is a unified, enterprise-grade platform designed to combine remote access, workflow automation, real-time data analytics, and security management into a single environment. Rather than juggling separate tools for reporting, monitoring, collaboration, and data management, users get a centralized workspace where all these functions coexist and communicate seamlessly.
Think of it as the digital equivalent of a control tower: it receives signals from every corner of your operational environment — cloud databases, APIs, third-party applications, remote devices — and translates that raw input into structured, actionable intelligence.
This isn’t a niche developer utility. RCSDASSK is actively used in sectors ranging from healthcare and finance to logistics, education, and IT infrastructure management.
How Software RCSDASSK Works
Understanding RCSDASSK’s architecture helps explain why it has gained traction so quickly. The platform is built on a modular framework, meaning each functional component — security, automation, analytics, collaboration — operates independently but shares a common data layer.
Here is a simplified breakdown of its operational flow:
- Data Ingestion — RCSDASSK connects to your existing systems through APIs and native integrations, pulling data from cloud databases, CRMs, ERPs, and IoT devices in real time.
- Processing Engine — The core engine normalizes and processes this data, applying filters, rules, and automation triggers you configure.
- Dashboard Layer — Processed data surfaces in customizable dashboards, giving teams a live view of KPIs, system health, and workflow status.
- Automation Execution — Scheduled or event-triggered tasks run automatically, from backup routines to compliance reports and alert dispatches.
- Security Monitoring — The platform continuously audits user activity, flags anomalies, and enforces role-based access controls.
This architecture ensures that even large organizations with complex, fragmented tech stacks can bring their data under a single operational roof — without rewriting legacy systems or hiring large IT teams.
Key Features of Software RCSDASSK
RCSDASSK’s feature set is one of its strongest competitive advantages. The following table outlines its core capabilities and the value each delivers:
| Feature | What It Does | Who Benefits Most |
|---|---|---|
| Real-Time Data Sync | Connects to APIs, cloud databases, and third-party apps, reflecting live data in dashboards | Operations teams, analysts |
| Automated Reporting | Generates scheduled or trigger-based reports without manual input | Managers, compliance teams |
| Remote Device Access | Securely control computers, servers, and mobile devices from anywhere | IT administrators, remote teams |
| Customizable Dashboards | Build role-specific views showing only the metrics that matter | All departments |
| Workflow Automation | Automate repetitive tasks like backups, updates, and notifications | Dev teams, HR, finance |
| Built-In Collaboration | Shared workspaces, document co-editing, task assignments, and messaging | Distributed and hybrid teams |
| AI-Driven Insights | Machine learning identifies patterns, predicts failures, and recommends optimizations | Enterprise IT, decision-makers |
| Security & Compliance | Role-based access, MFA, audit logs, encryption, and HIPAA/SOC 2 support | Healthcare, finance, legal |
| Modular Architecture | Add or remove modules based on business size and need | Startups to enterprises |
| Cross-Platform Support | Works on Windows, macOS, Linux, and mobile environments | All users |
Why RCSDASSK Is Getting Attention in 2026
The rise of RCSDASSK can be attributed to a broader industry problem: tool sprawl. The average mid-sized company in 2025 used over 130 different SaaS applications, according to industry analysts. This fragmentation increases licensing costs, reduces data visibility, and forces employees to context-switch constantly.
RCSDASSK addresses this by consolidating what typically requires five or more separate platforms into one integrated environment:
- A dedicated reporting tool → replaced by automated reporting module
- A separate monitoring platform → replaced by real-time performance tracking
- Third-party collaboration software → replaced by built-in team workspaces
- An independent remote access client → replaced by the built-in remote control system
- A standalone security scanner → replaced by continuous audit and compliance monitoring
For businesses tired of paying for fragmented tools that barely communicate with each other, the value proposition is clear and immediate.
Industry Use Cases
RCSDASSK isn’t a one-size-fits-all tool — its modular design means it adapts meaningfully across industries. Here are the most documented real-world applications:
Healthcare
Hospitals and clinics use RCSDASSK to manage patient records, automate compliance audits, and monitor system uptime across hospital networks. Its HIPAA-compliant data handling makes it a viable choice for environments where data security isn’t optional.
Financial Services
Banks and fintech firms rely on RCSDASSK for financial data analysis, fraud detection workflows, and automated document generation. The platform’s audit logs and role-based permissions align well with SOC 2 compliance requirements.
Logistics and Supply Chain
Logistics companies connect RCSDASSK to vendor tracking systems and inventory platforms. When stock levels drop below defined thresholds, the system automatically triggers reorder requests and notifies relevant teams — with no manual intervention.
IT Departments
IT teams use RCSDASSK for remote server management, software deployment pipelines, and network monitoring. For teams running microservices or distributed systems, the real-time visibility across services is particularly valuable.
Education
Educational institutions leverage RCSDASSK to manage student devices, monitor network usage, and provide secure tools for online learning environments.
Digital Marketing Agencies
Agencies automate content syncing across platforms, secure client data, and collaborate in real time — all without switching between separate tools.
System Requirements
Before installation, your environment should meet the following minimum and recommended specifications:
| Specification | Minimum | Recommended |
|---|---|---|
| RAM | 4 GB | 8 GB or more |
| Processor | Dual-core, 2GHz | Quad-core, 2.5GHz+ |
| Storage | 500 MB available | SSD with 2 GB+ |
| OS | Windows 10, macOS 10.15, Ubuntu 20.04 | Latest stable versions |
| Internet | Standard broadband | High-speed for cloud sync |
How to Install and Set Up Software RCSDASSK
The installation process is designed to be approachable for both technical and non-technical users. Here are the steps:
Step 1: Download the Package
Obtain the installer from the official RCSDASSK source. Always verify you are downloading from a trusted, official repository to avoid security risks.
Step 2: Run the Setup Wizard
Execute the installer and follow on-screen prompts. The setup wizard handles dependency checks and environment configuration automatically.
Step 3: Create or Sign In to Your Account
On first launch, create a new account or authenticate with an existing one. This account governs your permissions, data access, and billing tier.
Step 4: Configure Your Dashboard
Select the modules and data panels relevant to your role. The interface allows you to arrange widgets, add data sources, and set your preferred display format.
Step 5: Connect Your Devices and Data Sources
Use the device pairing feature to link servers, computers, and mobile devices. For data integration, connect your cloud databases and third-party APIs through the built-in connector library.
Step 6: Set Up Automation Rules
Use the automation wizard to define scheduled tasks — backups, system scans, software updates, or custom event-triggered workflows.
Step 7: Invite Your Team
For collaborative environments, send email invitations to team members and assign role-based permissions to control access levels.
Understanding and Fixing the RCSDASSK Error Code
Alongside the software itself, many users encounter “Codes Error RCSDASSK” in system logs, CI/CD pipelines, or cloud-based services. This is a separate but related topic worth understanding clearly.
What Causes the RCSDASSK Error?
The error is typically a configuration or compatibility issue, not a security threat. Common root causes include:
| Error Trigger | Description |
|---|---|
| Incorrect config files | Structural errors or missing values in .env, config.yaml, or settings.json |
| Outdated SDK or dependencies | Older library versions incompatible with newer service endpoints |
| Expired or invalid API tokens | Authentication mismatches during remote service calls |
| Software dependency corruption | A broken package disrupts communication between modules |
| Kernel-level conflicts | Background service conflicts in Linux or Windows environments |
| Failed remote configuration delivery | Client-server mismatch during configuration sync |
Step-by-Step Fix Guide
Step 1: Restart the system — Many temporary conflicts resolve with a clean reboot.
Step 2: Check and repair system files — Use built-in OS utilities (like sfc /scannow on Windows or fsck on Linux) to identify and fix corrupted files.
Step 3: Update all packages and dependencies — For Node.js environments, run npm update. For Python, use pip install --upgrade for all relevant packages.
Step 4: Regenerate API tokens — Log into your service dashboard and reissue credentials if authentication is the suspected cause. Update all environment variables accordingly.
Step 5: Run in debug mode — Enable verbose logging to identify the exact point of failure in your execution chain.
Step 6: Check version compatibility — Ensure your SDK version is aligned with the service endpoints it communicates with.
Step 7: Contact official support — If all else fails, open a support ticket with relevant debug logs attached.
Important: Avoid applying unverified fixes from community forums without understanding the underlying cause. Quick patches without context often create secondary issues.
RCSDASSK vs. Competing Platforms
How does RCSDASSK stack up against other tools in its category?
| Criteria | RCSDASSK | Traditional Monitoring Tools | Generic Automation Platforms |
|---|---|---|---|
| Unified workspace | ✅ Yes | ❌ No | Partial |
| Real-time data sync | ✅ Yes | ✅ Yes | Partial |
| Built-in collaboration | ✅ Yes | ❌ No | ❌ No |
| Remote access | ✅ Yes | ❌ No | ❌ No |
| Security & compliance | ✅ Built-in | Add-on required | Add-on required |
| AI-driven insights | ✅ Yes | Limited | Limited |
| Modular scalability | ✅ Yes | Limited | ✅ Yes |
| Cross-platform support | ✅ Yes | Varies | ✅ Yes |
Pros and Cons
No platform is without trade-offs. Here is an honest assessment:
Strengths:
- Consolidates multiple tools into a single environment, reducing licensing costs and context switching
- Real-time data visibility across connected systems and devices
- Security and compliance features are built in, not bolted on
- Modular architecture makes it accessible for small teams while scaling to enterprise needs
- AI-powered insights reduce the burden on human analysts
Limitations:
- The initial setup and configuration can be complex for non-technical users
- Advanced features may require a learning curve and possibly dedicated training
- Premium tiers can be cost-prohibitive for very small businesses or solo freelancers
- Customization depth, while powerful, can feel overwhelming without clear use-case definition
Security Best Practices When Using RCSDASSK
Given that RCSDASSK operates as a hub for sensitive operational data, security hygiene is non-negotiable. Here are the practices that matter most:
- Always download from official repositories — Avoid third-party distributions that may bundle modified or compromised versions.
- Enable multi-factor authentication — Especially for admin accounts with elevated permissions.
- Regularly rotate API keys and access tokens — Expired or stale credentials are one of the most common entry points for unauthorized access.
- Apply updates promptly — Many critical patches address vulnerabilities in background services.
- Use role-based access controls — Limit each team member’s access to only the data and modules their role requires.
- Maintain audit log reviews — RCSDASSK’s built-in audit trail is only valuable if someone actually reviews it periodically.
According to the U.S. Cybersecurity & Infrastructure Security Agency (CISA), misconfigured services remain among the most common causes of organizational vulnerabilities — making proper RCSDASSK configuration a genuine security priority.
The Future of RCSDASSK
The platform’s development roadmap points toward deeper AI integration and greater autonomy. Planned enhancements include expanded natural language processing for interface interactions, voice-activated commands, machine learning customization that adapts to individual business models, and enhanced offline support for environments with limited connectivity.
The longer-term vision positions RCSDASSK as a fully autonomous management assistant capable of decision support, predictive resource allocation, and self-healing workflows — where minor errors are detected and corrected without human input. For organizations planning technology investments with a multi-year horizon, this trajectory is worth factoring into platform selection decisions.
Frequently Asked Questions
Q: Is software RCSDASSK safe to use?
Yes, when downloaded from official sources and configured following best practices, RCSDASSK is regarded as a secure platform. It supports encryption, MFA, and continuous audit monitoring.
Q: Is the RCSDASSK error code a virus or malware?
No. The codes error RCSDASSK is a configuration or compatibility error, not a security threat. It does not indicate malware presence.
Q: Can small businesses use RCSDASSK?
Yes. Its modular design allows small teams to start with basic features and scale as needs grow. A free tier is available for freelancers and small teams.
Q: Does RCSDASSK work with existing tools like CRM and ERP?
Yes. The platform supports API-based integration with a broad range of third-party applications including CRM, ERP, and analytics platforms.
Q: What operating systems does RCSDASSK support?
RCSDASSK supports Windows 10 and above, macOS 10.15 and above, Ubuntu 20.04 and above, and mobile platforms through its cloud-based access layer.
Q: What should I do if the RCSDASSK error persists after troubleshooting?
Open a support ticket with your official service or API provider, and attach the verbose debug logs captured during troubleshooting sessions.